Spark eDiscovery Blog
eDiscovery in Real Life
How to find a niche
I was very happy to write an article for the American Bar Association’s GPSolo Magazine this month! The issue was about alternative legal career paths, and included academia, real estate, tax, recruiting, coaching, HR, ADR, and … eDiscovery.
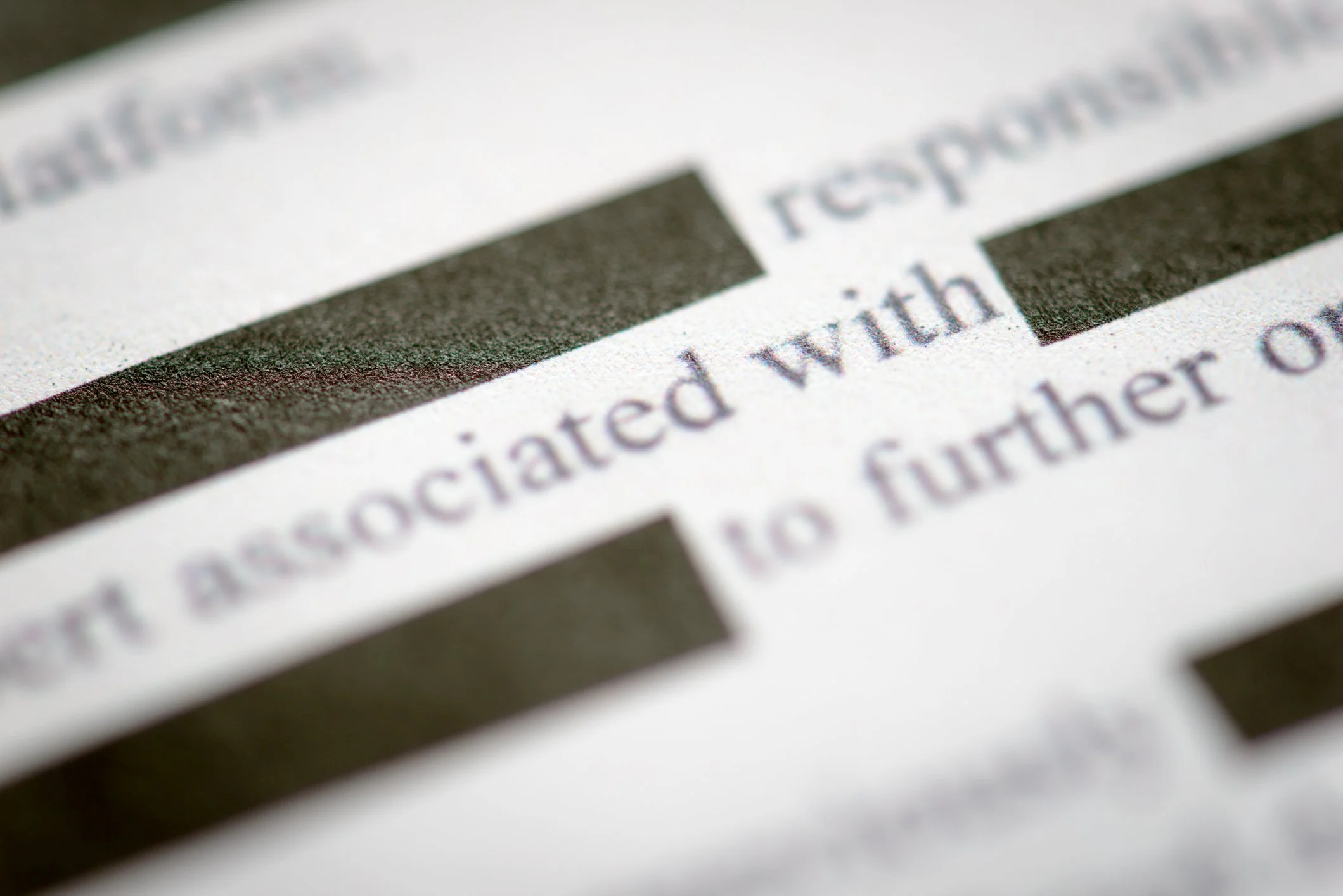
No one had to “hack” the Epstein Files. DOJ failed to actually redact them.
DOJ’s careless release of victim information in the Epstein Files was easily avoided. They knew better, and so should you.

In 2025, Let’s Make Active Learning a Part of Your Team
Happy New Year! It is 2025, and it’s time to use the best AI available, usually for little cost, to assist all document reviews. It is time to apply Active Learning to every review project, every time.


Does the standard review protocol need to change to find treasure in short message data?
Say the case’s “silver bullet” document is a chat between defendants. Figuring out whether this is a relevant and responsive document requires understanding the abbreviation, the timing of the conversation, the roles of the participants, and perhaps the anxiety conveyed by the emoji. A reviewer in the last days of the review may have developed this context and will recognize the importance, but what if the chat surfaced on day one of the review? It might not have been identified as key … or it might not have been identified as responsive at all.
Should we change the review process to account for this disconnect? This is a conversation that the tech-focused side of the aisle often misses, and an ongoing one. Here are a few of my thoughts on how we can ensure short messages don’t fall through the cracks.


The “Perfect Date”
Just in time for Valentine’s Day, Spark brings you: The Perfect Date? An small adventure in Metadata.
Avoid getting an “Undifferentiated Pile” production
You served 10 Requests for Production on the opposing party under Fed. R. Civ. P. 34.
Finally, after months of harassment, they have given you a single, 500-plus-page PDF file, with Bates-stamped pages.
You're going through it, and both you and your computer are losing the will to live.
Sound familiar? Productions like this are the norm in smaller cases and certain practices. But such low-tech production of ESI (electronically-stored information) in discovery almost certainly violates Fed. R. Civ. P. 34.

Privilege, Attachments, and an ESI Protocol Surprise
In a recent case, opposing counsel added a new term to the ESI Protocol that I had not seen before. It required us to separately log each document withheld for attorney-client privilege, including email attachments, and provide an independent basis for privilege for each document.
This term threw me off.

Why can’t my client just forward me the relevant emails for discovery?
Is your client’s CEO leery about letting attorneys go digging through his inbox? We would be too. But in all but the smallest cases, it is improper to leave it up to the client to decide where to look and what is responsive.
![Dance with the [vendor] that brought you.](https://images.squarespace-cdn.com/content/v1/62c72a1ad6f918292d8698e1/1665101845486-TZPUARGQLVUE84LSVFDB/Distracted+Boyfriend+meme.jpeg)
Dance with the [vendor] that brought you.
Despite good-faith efforts from the new vendor and the in-house technical team from the old firm, it took me months to iron out the issues that this seemingly-simple decision introduced. Unless the situation with your existing vendor is untenable, don’t change horses mid-stream!

Déjà views? A brief look at methods for cutting down on duplicates.
“We have seen so many of the same document! Can’t we deduplicate?”
Yes, but!